How to Build a Fintech MVP in 2026: What Nobody Tells You
Building a fintech MVP? Here's what most founders get wrong — from payment rails to KYC architecture. A practitioner's guide from a team that's shipped it.
In April 2024, a fintech company called Synapse filed for bankruptcy. By July, $160 million in customer funds were frozen. Nearly 100 startup founders woke up to find their products had stopped working overnight — not because of bugs, not because they ran out of money, but because of one infrastructure dependency they hadn't fully stress-tested when they chose it two years earlier. Andreessen Horowitz had called Synapse "the AWS of banking." Copper, a teen banking startup built on top of it, had to shut down every deposit account and debit card it had ever issued. Mainvest, a fintech lender, shut down entirely.
Nobody's fintech MVP failed because the code was bad. They failed because the decisions made in week two — which payment rails, which BaaS provider, which compliance architecture — turned out to be load-bearing walls, not scaffolding.
The question isn't whether your fintech MVP will face regulatory or infrastructure pressure. It's whether the foundational decisions you make in the first few weeks of fintech MVP development will survive contact with reality.
Here's what that actually looks like.
The Fintech MVP Myth
Most founders arrive with a version of the same plan: build the app, integrate Stripe or Plaid, drop a KYC provider into the onboarding flow, and launch. Clean. Simple. Fast.
What they don't realize is they've just described a product that may not be legal to operate in their target market.
Fintech is not a SaaS product with a payments button. It's a regulated financial service that happens to have software on top of it. The moment you're moving money — even if you're just facilitating a transfer, not holding funds yourself — you're operating in a regulatory environment that treats "we'll figure out compliance later" the same way a bank treats an overdraft: as a liability with compounding interest.
In 2026, regulators at the CFPB, FinCEN, and state money transmitter offices are not running discovery calls with early-stage startups. They've watched enough post-COVID fintech growth to recognize a scrappy MVP when they see one. "Test first, license later" is no longer a viable playbook. It gets you a cease-and-desist.
The invisible layer most developers won't warn you about: it's not the API integrations that break fintech MVPs. It's the architectural decisions that sit underneath every API you're calling.
5 Things That Kill Fintech MVPs Before Launch
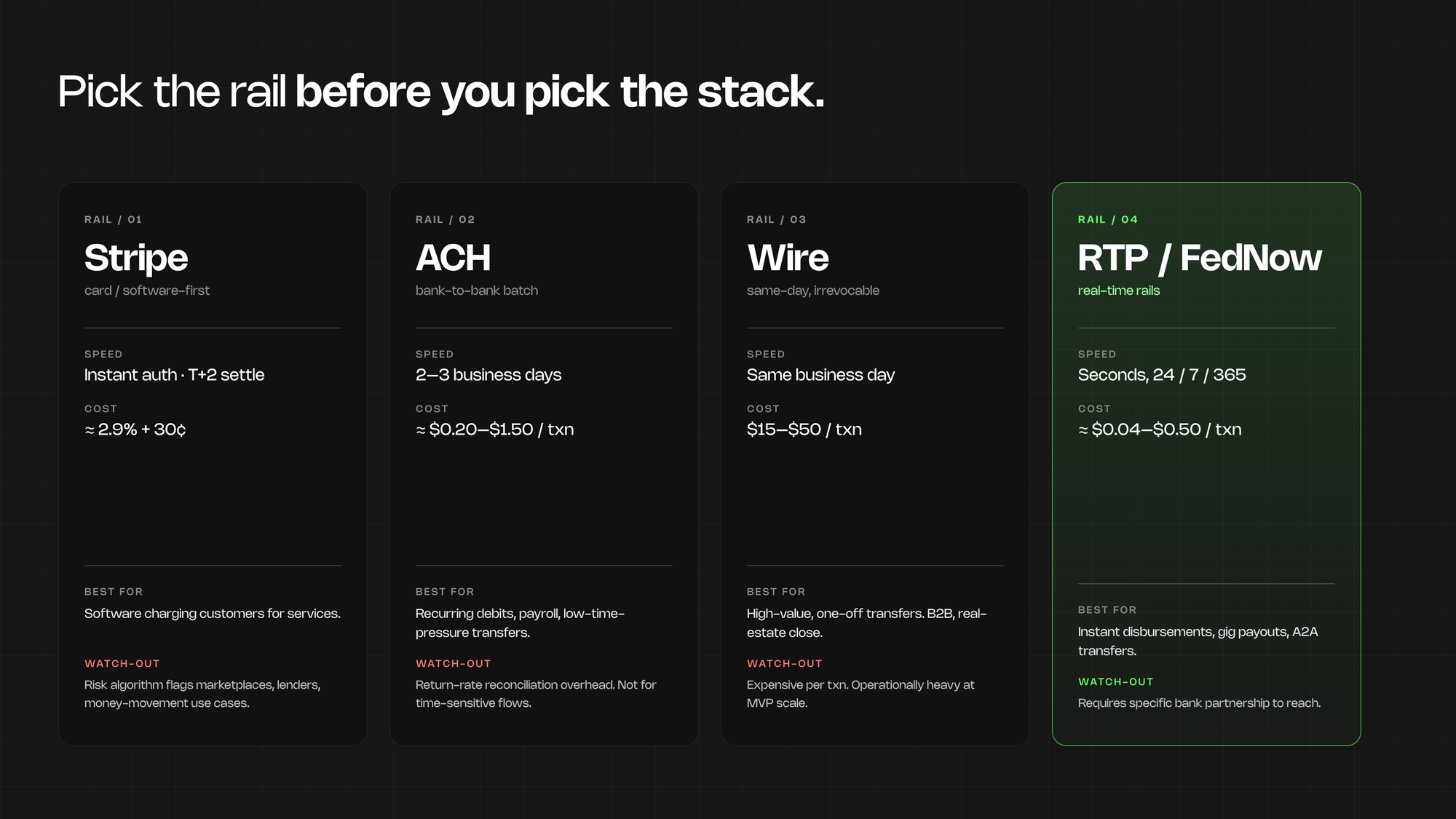
1. Picking the wrong payment rails
Stripe, ACH, wire transfers, and embedded banking are not interchangeable. They're designed for fundamentally different use cases — and choosing the wrong one doesn't just limit your product, it can invalidate your entire business model.
Stripe works well for software-first businesses charging customers for services. It was not designed for platforms that facilitate money movement between third parties, hold funds on behalf of users, or operate in regulated verticals like lending or investing. Build on it for those use cases and you will eventually hit their risk algorithm. Your account gets flagged. Support takes days to respond. Your launch is in two weeks.
ACH is cheap and universally supported — but settlement takes 2 to 3 business days, return rates create real reconciliation overhead, and it's not built for time-sensitive transactions. Wire transfers are fast but expensive per transaction and operationally intensive at scale. Real-time rails like RTP and FedNow are increasingly accessible but require specific bank partnerships to reach.
The payment rail decision affects your unit economics, your user experience, your fraud exposure, and which licenses you'll need to operate. It's not a technical detail you can revisit in sprint 6.
2. KYC and AML as afterthoughts
Know Your Customer and Anti-Money Laundering compliance are not features you layer into onboarding in sprint 4. They're architectural requirements that shape your data model from day one.
Global AML and KYC penalties hit $4.5 billion in 2024. Deepfake-based identity fraud attempts in the US are up over 1,100% since early 2025. Regulators are not in a forgiving mood, and your bank partners — the ones providing the actual financial infrastructure underneath your product — are under increasing pressure to enforce compliance on the fintechs they serve.
The practical problem is this: if your database schema wasn't designed to store the audit trail your compliance obligations require — transaction histories, identity verification results, adverse media screening records, beneficial ownership data — you'll find out in the worst possible context. A bank partner review. A regulatory exam. A due diligence call with your Series A lead.
Not a feature gap. A rebuild.
There's also a conversion rate dimension that founders consistently underestimate. KYC drop-off during onboarding varies from 5% to 40% depending on provider and implementation. That's not a UX problem you can A/B test around later. It needs to be scoped before you write the first screen.
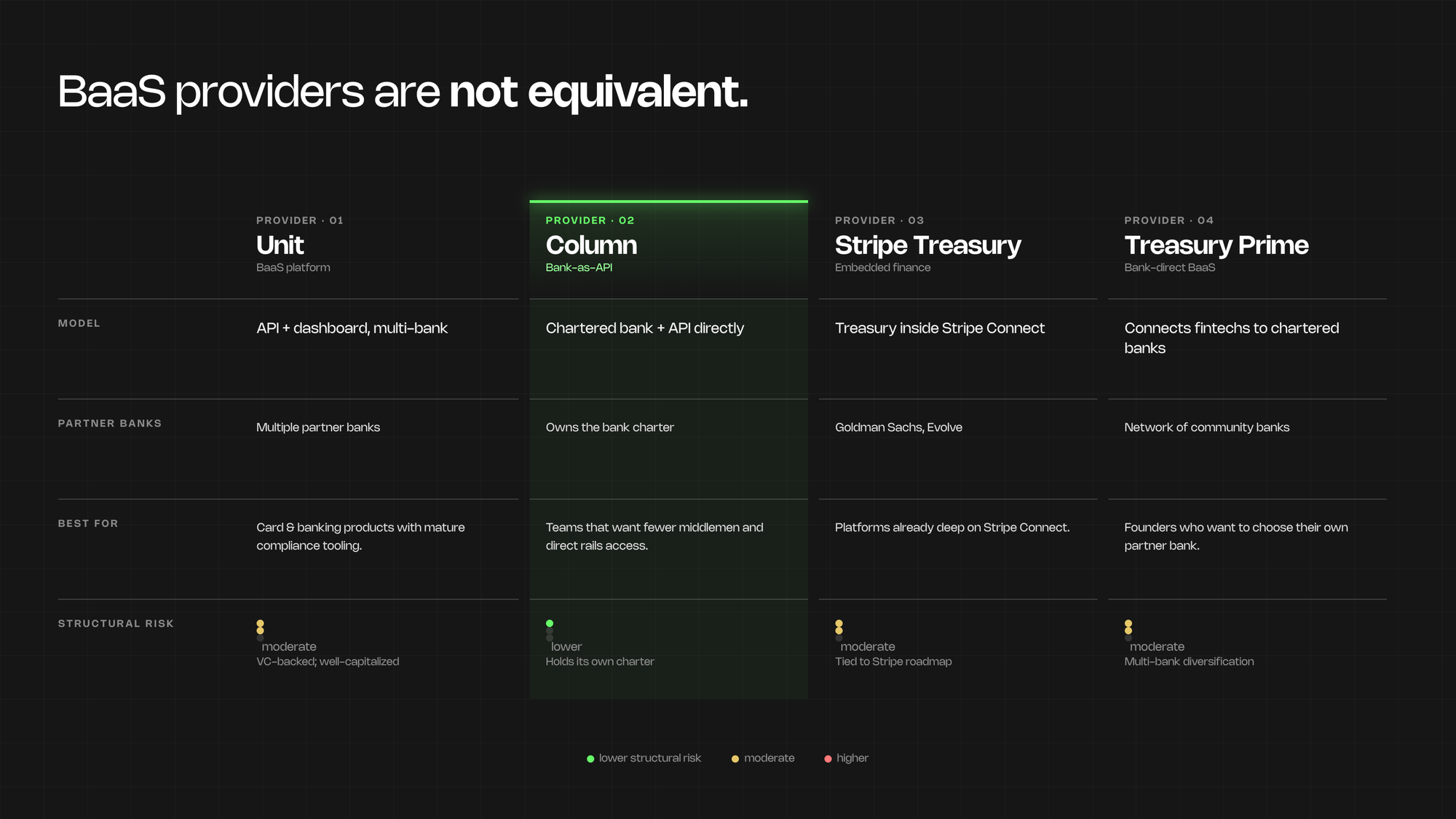
3. BaaS provider lock-in and risk exposure
The Synapse story isn't an edge case. It's what happens when you treat your BaaS provider as a commodity vendor rather than a critical dependency that deserves the same scrutiny as a co-founder.
Banking-as-a-Service providers — Unit, Column, Stripe Treasury, Treasury Prime, and others — are not equivalent. They differ in risk appetite, partner bank relationships, supported use cases, pricing, and frankly, survival probability. Some are profitable businesses with long bank relationships. Some are venture-backed startups burning toward their next raise. Synapse had $51 million in VC funding and a16z's endorsement. It still filed for Chapter 11.
The fintechs that came through Synapse's collapse with their businesses intact were the ones who understood exactly which parts of their product depended on Synapse's infrastructure. Most didn't know until it stopped working.
When evaluating BaaS providers, the questions that matter aren't just about API quality. Ask about their partner bank relationships and what happens if one of those banks changes its risk posture. Ask about their regulatory track record. Ask what the offboarding process looks like if you ever need to migrate. A provider who can't answer those questions clearly is a structural risk to your business, not just a vendor.
4. The compliance-first architecture paradox
Nobody talks honestly about the trade-off here: building compliance-first takes longer. And cutting compliance corners will take longer to fix later, at a worse time.
Founders who want to move fast aren't wrong. Speed matters. Getting to real users matters. But fintech has a higher minimum viable compliance threshold than almost every other product category. You can ship a SaaS MVP with basic email/password auth and add SSO in month 3. You cannot ship a payments product and add your AML transaction monitoring in month 3 — not without rebuilding core infrastructure underneath a live product that's handling real customer money.
The answer isn't maximum compliance in v1. It's architecting for compliance from the start, even if you're not implementing all of it immediately. That means choosing the right data model before you write any application code. It means selecting your BaaS provider and KYC vendor before your engineers start writing API integrations. It means knowing your regulatory surface area before you scope your engineering work.
Architecture decisions made in week two are almost always more expensive to reverse than architecture decisions made in month three.
5. Scope creep from unmapped regulatory requirements
This one catches founders who've done everything else right.
Money transmitter licenses are required in most US states the moment you're moving money. Each state has its own application process. Applications take 6 to 18 months per state, require capital reserves, documented compliance programs, audited financials, and executive background checks. If your business model requires them and you discover this in month 4 of development, you're looking at a minimum 12-month delay before you can legally operate at scale in your target markets.
The same logic applies to state lending licenses, broker-dealer registrations, and investment advisor requirements, depending on your vertical. Each brings its own application timeline and ongoing reporting obligations.
One fintech founder I know treated compliance as a post-launch problem when building his peer-to-peer lending platform. The detour cost him $85,000 and eight months. That story is common enough that it probably sounds familiar.
Mapping your regulatory surface area before you scope your engineering work is not a luxury. For fintech, it's the difference between a 4-month build and an 18-month ordeal.
What a Compliant Fintech MVP Actually Looks Like
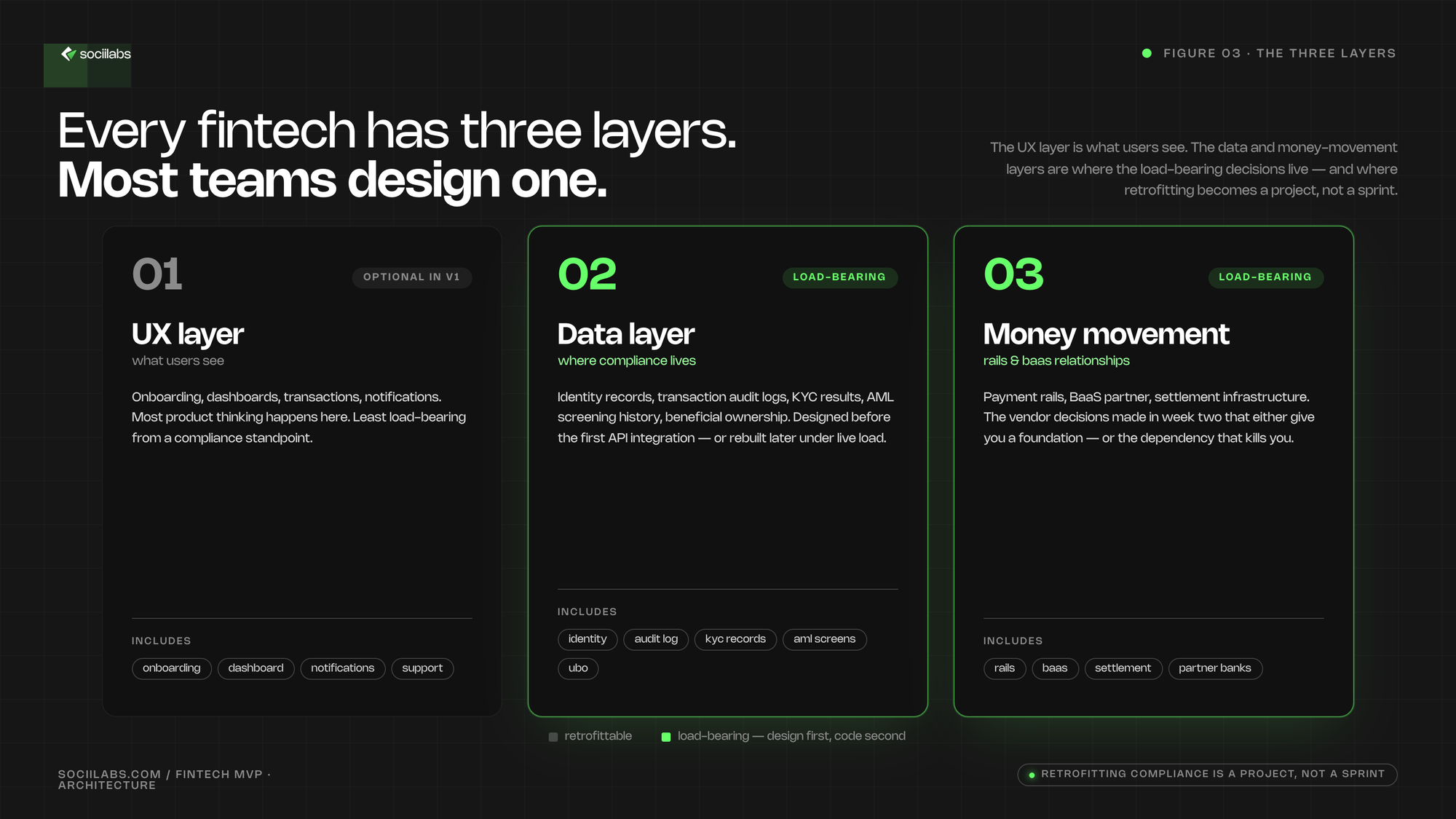
Every fintech product has three layers, and most founders only design one of them.
The UX layer is what your users see: onboarding, dashboards, transaction history, notifications. This is where most product thinking happens, and it's the least complicated layer from a compliance standpoint. Nice to get right, but not where the load-bearing decisions live.
The data layer is where your compliance obligations live: identity records, transaction audit logs, KYC verification results, AML screening history, beneficial ownership data. This layer needs to be designed before you write a single API integration. Once you've built your data model without compliance requirements in mind, retrofitting it isn't a sprint. It's a project that runs alongside your live product.
The money movement layer is your payment rails, BaaS relationships, and settlement infrastructure. This is where the vendor selection decisions you make in week two — often based on "what can I get running fastest" — will either give you a scalable foundation or create the structural dependency that kills you when something upstream changes.
Realistic build timeline for a well-scoped fintech MVP: 3 to 4 months for payments-adjacent products where the compliance architecture is established before engineering starts. Longer for lending, insurance, or anything requiring state-by-state licensing. The 4-week MVP frameworks written for SaaS do not apply here.
On the 2026 tech stack: sensible defaults for most fintech MVPs are Unit or Column for BaaS (both have mature compliance tooling and established bank partnerships), Persona or Onfido for KYC, and Sardine or Unit21 for fraud and AML monitoring. Your specific use case shapes this — but "which Stripe product should I use" is the wrong starting question.
How to Scope a Fintech MVP Right
Every fintech startup MVP scoping process starts with the same question: are you moving money, facilitating money movement, or neither?
Moving money — you hold customer funds, execute transfers on their behalf, or issue financial instruments like cards or accounts. This carries the highest regulatory load. You need BaaS infrastructure, a licensing strategy, and compliance architecture from day one.
Facilitating money movement — you're connecting parties, providing financial data, or operating a marketplace without holding funds directly. Less regulation, but more complexity in how you interact with the money movement infrastructure beneath you.
Neither — financial data tools, planning software, analytics. Lighter compliance surface. This is where you actually can move faster.
Build vs. buy for compliance comes down to three options: acquire a licensed entity (expensive, but fast-tracks market access), operate under a BaaS provider's license (faster to start, but creates the dependency risk we've covered), or apply for your own licenses (slowest, maximum control). Most early-stage fintech MVPs should launch on a BaaS provider's paper — but they should choose that provider with the same rigor they'd apply to hiring a CTO.
The "compliance minimum viable product" is not a shortcut. It means building what's legally required to operate your v1 use case in your initial markets — and nothing less. Mapping that precisely, before you scope your engineering sprints, is how you avoid the compliance detour that adds months and six figures to your build.
When to Hire a Specialized Team
Generic development shops fail at fintech for a specific reason: they treat it like SaaS with extra steps. The API integrations aren't hard. The compliance architecture, the BaaS selection criteria, the regulatory surface area mapping — that's where generalists become expensive.
When evaluating a fintech development partner, the conversation should surface these signals quickly:
- Do they ask about your licensing strategy before they ask about your stack?
- Have they built on multiple BaaS providers and can speak to the trade-offs between them?
- Can they scope your compliance minimum viable product before writing the first line of code?
- Do they have vendor opinions on KYC providers based on your specific onboarding use case — not just whatever's easiest to integrate?
A discovery sprint before a fintech build isn't due diligence theater. For this category, it's where the foundational decisions actually get stress-tested: regulatory surface area, BaaS provider vetting, data model for compliance, payment rail selection. Founders who skip it are the ones rebuilding in month 6, while their competitors are onboarding their first 500 users.
We've shipped fintech products across payments, lending, and banking-as-a-service. We've made the architecture mistakes so our clients don't have to, and we've learned which foundational decisions have the longest blast radius when they're wrong. If you're building a fintech product and want to map the architecture before you start the clock on your engineering budget, that's exactly what we do.
Building a fintech product? We've navigated payment rails, KYC, and compliance-first architecture before. Book a call →
Not ready for a call? Run the numbers on your build →